
Security-conscious Windows users attempting to protect themselves against Meltdown and Spectre attacks in the wild are being met with a deceptive “Your device is up to date” message — but they’re not yet protected.
In the days following the disclosure of CPU cache attacks Meltdown and Spectre, hardware, kernel, and software developers have rushed to provide security updates for their respective devices and platforms in an (ongoing) effort to secure their users against the wide-ranging (and not yet fully understood/internalized) side-channel vulnerabilities disclosed a few days ago on the 3rd of January, 2018.
For those that aren’t up to date on these attacks – stop now, and read this excellent LWN article on Meltdown and Spectre; if you’re so inclined, you can even have a look at the original Google Project Zero article where it all started.1
Meltdown and Spectre recap
The short and tall of it all is that an entire class of security vulnerabilities – known as side-channel attacks – suddenly went from “things your mother used to tell you to make you behave at night” to “there’s a serial killer loose in your apartment and all the doors are locked” kind of scary. Side-channel attacks, despite what the hysterical coverage surrounding Meltdown and Spectre would have you believe, are nothing new, and have been heavily researched for decades.23456
There is sufficient coverage – and people far more qualified to provide it – surrounding both of these vulnerabilities all over the internet (perhaps too much coverage, if only because when CNN Money covers a netsec article, they’re likely to get things wrong) but in our opinion what really matters right now to end users is not “what this bug is” or even “what’s being done about it” but just “what should I do to keep myself protected?”
Hardware and OS vendor response
Unlike the majority of security bugs that are published on a daily basis, one of things that makes both Meltdown and Spectre scary is that they potentially affect virtually every computer, from the workstation we’re writing this article on, to the server hosting it, to the desktop, laptop, or even cellphone you’re reading this on. These bugs affect – to controversially varying extents – all hardware, platform, and software combinations, and require updates on all fronts to fully secure users from malicious attackers seeking to capitalize on these vulnerabilities for their own self-serving, twisted purposes. This includes Intel, AMD, and ARM; Windows, macOS, and Linux; iPhones, Androids, Blackberries, and everything in between.
Intel and AMD have been scrambling to provide hardware updates (Intel probably more so than AMD, given that Intel has severely dropped the ball on CPU security when compared to its competitors) known as “microcode updates” that are basically the equivalent of a software patch for your CPU. These are applied either permanently via a BIOS/firmware update available from your motherboard manufacturer (so most people can just give up on ever seeing those unless they have an incredibly recent PC) or hardware maker (in the case of iPhones and Androids, the latter of which will be under extreme pressure as they’re particularly notable for almost never providing security updates to their users outside of a few months from the release date in most cases), or they can be applied “dynamically” at system startup by your operating system, if it detects an out-of-date microcode version on your CPU and it has a newer version available that it can “soft patch” your PC with.
Microsoft’s (tepid) official response
All of which brings us to the ultimate point of this article: while Project Zero made vendors and manufacturers aware of this vulnerability in July of 2017, giving both plenty of time to create and test the needed updates (as they are far-reaching and tackling them efficiently presented a particularly onerous challenge), it does not seem to have been sufficient. While Apple patched iOS to mitigate the effects of and susceptibility to Meltdown/Spectre with iOS 11.2 (released December 3, 2017), Microsoft’s fix for Windows 10 PCs was not published until the 3rd of January, 2018 as KB4056892 – and won’t actually be pushed out to all PCs opting into Windows Update until the 9th of January (aka “Patch Tuesday”), a full week after the public disclosure of the vulnerability. This is despite famed NT kernel developer Alex Ionescu publicly confirming Windows’ equivalent to Linux’s kernel page table isolation (pti) fix from mid-November of last year.
Even more so, in a move catering to 3rd-party antivirus vendors over their users, after discovering that many 3rd-party AV products would fail to work (or cause your PC to fail to work) in the presence of this upcoming patch, Microsoft has opted to defer to the developers of these antivirus products to set a flag in the PC registry that would indicate that the PC is “ready to receive the update” rather than making the Meltdown/Spectre fix an optout-only kind of deal.
In short, from January 3rd until January 9th, Windows users will be easy targets for the picking and it would not surprise us in the least to learn that proprietors of less-than-savory websites have already implemented JavaScript-based attacks to target vulnerable Windows users, attempting to capitalize on this window of opportunity wherein a huge segment of the online population is completely unprotected against a vulnerability that could easily7 steal passwords from your browser just by merely visiting a website with this attack in its page code.
Protecting against Meltdown
What can you do about this? Glad you asked. Before anything else, if you’re using Google Chrome or Mozilla Firefox – update your browser (or make sure it has automatically updated). One of the scariest things about Meltdown is that it can – and not just in theory – be exploited from the browser, without running any code on your PC in the traditional sense.8 If you’re using Microsoft Edge or Internet Explorer 11 – unfortunately the best advice we have right now is, don’t. Microsoft’s browsers don’t currently receive updates out-of-band from the OS, and will remain vulnerable/unpatched until the January 9th/Patch Tuesday.
With regards to ensuring that your Windows installation itself has the needed updates to mitigate against the effects of Meltdown (and Spectre), Microsoft’s official instructions here are unfortunately less than ideal: in addition to being rather not security conscious, they’re also on the cryptic side.
The published guidelines explain how to check if your antivirus software has configured your PC as “ready to receive the patch” (applicable to users of both 3rd party antivirus products and Microsoft’s own Windows Defender), which involve searching the registry for a cryptically named entry (cadca5fe-87d3-4b96-b7fb-a231484277cc under HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\QualityCompat) and creating it if it doesn’t exist, then verifying that your PC’s security configuration is set to accept this update, including disabling corporate Windows Update configuration policies and temporarily overriding the Windows Insider configuration in order to guarantee that the update will be picked up and installed… come January 9th.
To make things more confusing, it appears that Microsoft’s website is somewhat “post dated” in that the instructions presume that “today” is past the official publication of the Meltdown/Spectre mitigation patch on January 9th: The instructions direct users on what to do if their PC isn’t picking up the update, but make no mention of the fact that the update isn’t actually live yet, and won’t be for another week.
In terms of OS updates, to make things considerably easier we’ve compiled a list of links to the update in question that should be installed on Windows PCs to mitigate against Meltdown and Spectre. Note that not all platforms are receiving this update, users of Windows XP and Windows Vista do not appear to be receiving this update (but then again, if you’re still on Windows XP or Windows Vista, you’re likely already vulnerable – if not even compromised – due to the countless other unpatched issues), and while we have a direct link to the Windows 7 patch, we haven’t yet found the revelant patch for Windows 8 and Windows 8.1 users, and it is unclear at this time whether a patch for those platforms is forthcoming. Additionally, a patch for Windows users on ARM64 platforms (mainly tablets) is only available for the latest Windows release (16299 aka “Fall Creators Update”) and not for any previous versions.
Meltdown/Spectre patch download links for Windows users
Confusingly, rather than a separate KB with different downloadables/payloads for each operating system, Microsoft is publishing their mitigation for Meltdown/Spectre as a series of separate KBs, each applicable to different systems. These are not just split at the major OS version level (e.g. Windows 7 vs Windows 10) but rather at the kernel version; a separate update exists for each “point release” (for lack of a better/universally-accepted word in Microsoft nomenclature) for each operating system; the fix will not apply if your operating system does not match the version it was intended for. Installation instructions continue after the download links below.
Security Note: while we were unable to locate any HTTPS links for these updates, the links below point to the official Microsoft Windows Update servers and (most importantly) the downloads themselves are all digitally signed by Microsoft. Never install unsigned OS updates.
KB4056892: Windows 10 1709 “Fall Creators Update” (Build 16299)
- 64-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-x64_a41a378cf9ae609152b505c40e691ca1228e28ea.msu
- 32-bit: http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-x86_d3aaf1048d6f314240b8c6fe27932aa52a5e6733.msu
- ARM64: http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-arm64_028810421e6036f439add546e189219649140f4b.msu
KB4056891: Windows 10 1703 “Creators Update” (Build 15063)
- 64-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056891-x64_59726a743b65a221849572757d660f624ed6ca9e.msu
- 32-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056891-x86_5e2d98a5cc9d8369a4acd3b3115789a6b1342159.msu
KB4056890: Windows 10 1607 “Anniversary Update” (Build 14393)
- 64-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056890-x64_1d0f5115833be3d736caeba63c97cfa42cae8c47.msu
- 32-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056890-x86_078b34bfdc198bee26c4f13e2e45cb231ba0d843.msu
KB4056888: Windows 10 1511 “November Update” (Build 10586)
- 64-bit: http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056888-x64_4477b9725a819afd8abc3e5b1f6302361005908d.msu
- 32-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056888-x86_0493b29664aec0bfe7b934479afb45fe83c59cbe.msu
KB4056893: Windows 10 1507 “Initial Release” (Build 10240)
- 64-bit: http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056893-x64_d2873bb43413d31871ccb8fea213a96a714a6f87.msu
- 32-bit: http://download.windowsupdate.com/c/msdownload/update/software/secu/2018/01/windows10.0-kb4056893-x86_b2a28dc6845c85fd32dcd511e3f73f82e46d355f.msu
KB4056890: Window Server 2016
KB4056987: Windows 7
- 64-bit: http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows6.1-kb4056897-x64_2af35062f69ce80c4cd6eef030eda31ca5c109ed.msu
- 32-bit: http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows6.1-kb4056897-x86_bb612f57e082c407b8cdad3f4900275833449e71.msu
More links will be provided as this list is updated
Installing Meltdown and Spectre patches on Windows
- After identifying the download link above that is applicable to your system, click the link to download the update to your PC. If you are prompted to open or save, choose “save”.
- Once the download has completed, double-click the downloaded file (the filename varies depending on your version of Windows, but it’s a long filename and it should up as “Microsoft Update Standalone Package” type) to begin the update process.
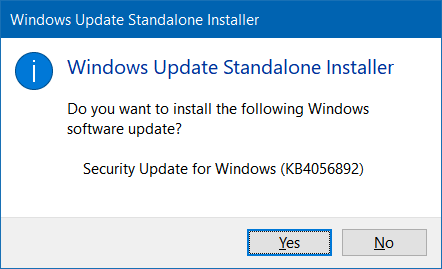
- The first thing the downloaded KB patch will do is verify the integrity of the download to make sure that the downloaded completed successfully; presuming it has, you’ll see the following dialog where you should choose
Yesto proceed with the update:
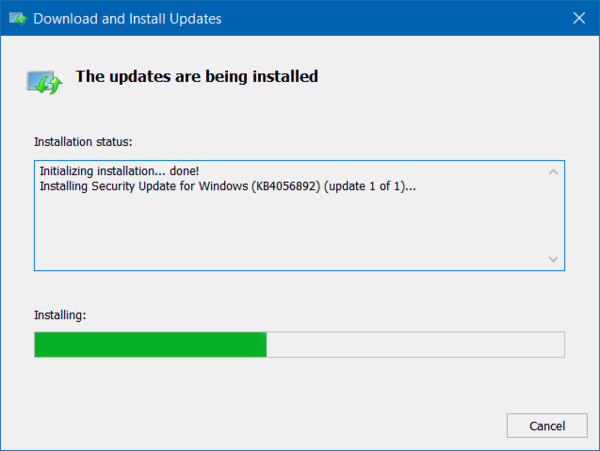
- The update process should begin at this point, and continue without needing any further user interaction:
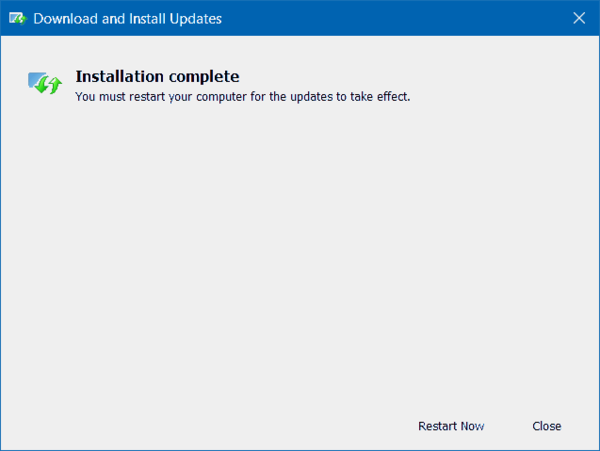
- Once the installation has completed, a dialog will present informing you that a reboot is required to fully protect your PC. You must reboot for the update to take effect. Choose
Restart Now, and your PC will reboot automatically to complete the update process.
Verifying Meltdown and Spectre mitigation status
Microsoft has released official instructions for verifying that the update has been installed correctly, but it is an involved procedure that will require familiarity with the command line and some use of PowerShell scripting, we are working on a simpler and more straightforward utility for our users.
While the latter is more technical in nature, programming-inclined readers in the audience may find it to actually be easier to grok with its more definite and concrete approach, vs the somewhat abstract nature of pretty much all the other coverage out there. ↩
Cache Attacks and Countermeasures, Dag Arne Osvik, Adi Shamir, and Eran Tromer; 2005 ↩
Side Channel Cube Attacks on Block Ciphers, Itai Dinur and Adi Shamir, 2009 ↩
RSA Key Extraction via Low-Bandwidth Acoustic Cryptanalysis, Daniel Genkin, Adi Shamir, and Eran Tromer; 2013 ↩
Last-Level Cache Side-Channel Attacks are Practical, Fangfei Liu, Yuval Yarom, Qian Ge, Gernot Heiser, and Ruby B. Lee; 2015 ↩
Cache side channel attacks: CPU Design as a security problem, Anders Fogh (the person most qualified to talk about anything related to the CPU cache), 2016 ↩
Although not stealthily, given the CPU requirements for the published JavaScript proof-of-concept attack to work, ↩
We’ll save the discussion about just how we ended up in a world where running untrusted/malicious bytecode in a potentially leaky sandbox is now considered “not running code locally” for another day. ↩

The article is incorrect. KB4056892 went out to Windows 10 users Friday.. It was originally scheduled for Jan 9 but was made available ahead of time when the publicity broke.
@Colin in our lab tests, that was not the case. This a screenshot from an affected (unpatched) system, running 16299, taken today:
(I just realized I don’t have the screenshot of the “this PC is not protected against Meltdown” from the speculative execution powershell script Microsoft posted at the time, but I can share that when I get back to a real PC.)
What leads you to think that these weren’t included in the monthly roll-up that was available on Windows update on 4th January?
For example KB4056894 for my Windows 7 Ultimate 64 bit.
I downloaded and run the standalone installer (KB4056892 Win 10 ver 1709-16299 x64) then I got the notice that the update is already installed. Does that mean I already installed the update earlier this week? If so, then no action is required on the PC other than the browser?
As a previous reader indicated, these updates were already pushed out early for all platforms, to include rollups and other patches; the article is vastly incorrect.
It means that MSFT released the KB yesterday instead of waiting until Tuesday. You have it installed normally.
It was.
I don’t think the script is working as hoped.
Error 404 – File or directory not found on the Windows 10 1709 Fall Creatorsupdate 32 bit version.
I got caught on an AMD computer yesterday by downloading KB4056892 and it wiped google chrome and all my e-mail info in thunderbird and at restart left me with just the blue windows logo and computer locked.I had to system restore and tried again and it did it again.I then found a link on the web to block this download for AMD computers at present.I then went to an Intel with 64 that I have and after downloading it told me it was already installed but I could not see it in list and yet 3 hours later it installed it itself and rebooted so you can’t go by the messages you get. Mervyn
I have been informed affected CPUs older than 5 years are not included and will give an error that your system is not compatible with the patch. Supposedly they will issue a patch for the older ones in some nebulous future.
Microsoft provided the necessary update on 5th Jan 2018. The article is BS.
De webpagina op http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-x86_d3aaf1048d6f314240b8c6fe27932aa52a5e6733.msu uitgeschakeld of permanent verplaatst naar een nieuw adres.
Webpagina http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-x86_d3aaf1048d6f314240b8c6fe27932aa52a5e6733.msu uitgeschakeld of permanent verplaatst naar een nieuw webadres.
De webpagina http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-x86_d3aaf1048d6f314240b8c6fe27932aa52a5e6733.msu uitgeschakeld of permanent verplaatst naar een nieuw webadres.
Melding: “http://download.windowsupdate.com/d/msdownload/update/software/secu/2018/01/windows10.0-kb4056892-x86_d3aaf1048d6f314240b8c6fe27932aa52a5e6733.msu uitgeschakeld of permanent verplaatst naar een nieuw webadres.”
As many others have noted, this article is a complete lie about Microsoft’s patch (KB4056892), in which it falsely claims that the company has left users unprotected until Jan 9..
On my own 7-year old AMD system, the patch was automatically downloaded and installed on Jan 3.
I already told everyone about this a couple months back and published how to block it.
In the Windows 7, there are the different type of reboot error can be detected and it has shown error code 0xc000000f
on the screen, and stopped working.