Hey! I know this has been brought up a few times, but I was unable to gather the information I need from the other threads.
I have a triple boot of Windows 7, Ubuntu and Windows 8, all installed on the same hard drive but in separate partitions. My Windows 7 will endure unrecognised software which may contain malware, I would therefore want to stop Windows 7 from accessing my main OS partition (Windows 8).
In other word I would like to hide Win8's partition from Win7. I have looked into NeoGrub which for some reason I was unable to install through EasyBCD. Are there other options to NeoGrub and which option would serve best in this situation? or should i keep trying to install NeoGrub?
Thanks
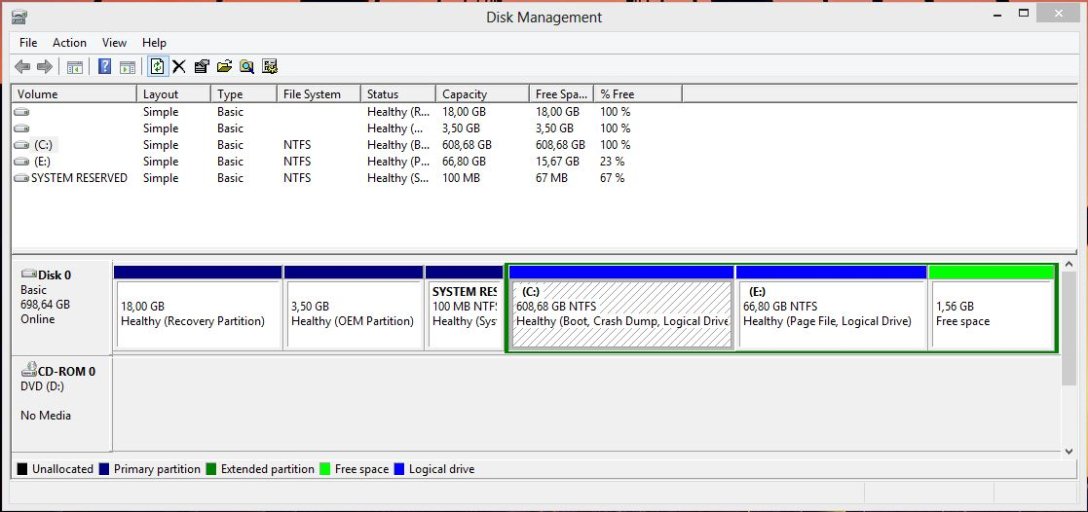
*My setup
I have a triple boot of Windows 7, Ubuntu and Windows 8, all installed on the same hard drive but in separate partitions. My Windows 7 will endure unrecognised software which may contain malware, I would therefore want to stop Windows 7 from accessing my main OS partition (Windows 8).
In other word I would like to hide Win8's partition from Win7. I have looked into NeoGrub which for some reason I was unable to install through EasyBCD. Are there other options to NeoGrub and which option would serve best in this situation? or should i keep trying to install NeoGrub?
Thanks
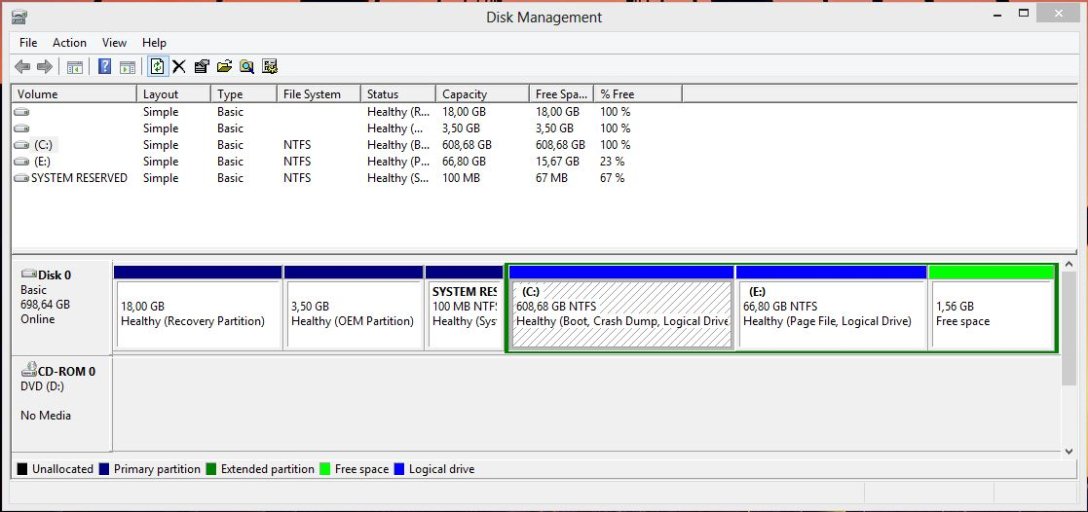
*My setup