SouthernCross
Member
Hello, I followed someone's suggestion of using a Standard Account for everyday use. So I went to Manage user accounts. And found 3 accounts listed:
-Andrew
-ASP.NET Machine Account
-Guest
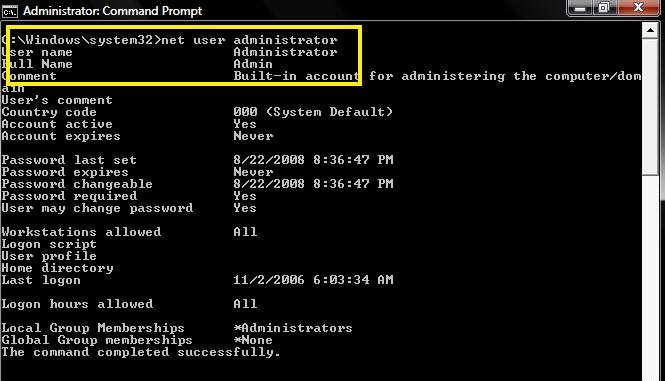
I assumed ASP.NET was part of Microsoft and was OK to use. So I set ASP.NET as the admin, and changed Andrew to a Standard User. Mistake. After a restart and some use, any UAC prompt requires a password for ASP.NET of which I do not know of. I've read that it generates random passwords. Also, I've tried safe mode to access Vista's back-up admin, it was a no go. Any help for setting Andrew back to admin?
-I cannot get through any UAC prompts.
-I cannot install most programs that require a UAC prompt.
-I do not have a Vista DVD due to it being pre-installed.
-I have not created a Recovery disc offered from HP. ...My fault.
-Safe mode does not show Vista's back-up Admin account.
-I run Vista HOME PRENIUM.
Any help?
-Andrew
-ASP.NET Machine Account
-Guest
I assumed ASP.NET was part of Microsoft and was OK to use. So I set ASP.NET as the admin, and changed Andrew to a Standard User. Mistake. After a restart and some use, any UAC prompt requires a password for ASP.NET of which I do not know of. I've read that it generates random passwords. Also, I've tried safe mode to access Vista's back-up admin, it was a no go. Any help for setting Andrew back to admin?
-I cannot get through any UAC prompts.
-I cannot install most programs that require a UAC prompt.
-I do not have a Vista DVD due to it being pre-installed.
-I have not created a Recovery disc offered from HP. ...My fault.
-Safe mode does not show Vista's back-up Admin account.
-I run Vista HOME PRENIUM.
Any help?