Long-time vim or neovim users are probably already aware that visually selecting a block of text then pressing CTRL + A in vim will result in any numbers in the selected block of text being incremented by 1. This works even if the block contains non-numeric text: each group of digits gets treated as a number and is incremented.1
For example, here’s a video that shows what happens when you select some text in vim and then use CTRL + A to increment the values:
To be pedantic, only the first group-of-digits/number on each line gets incremented; like many vim commands this only works on the first match per line of text unless some sort
/gglobal modifier is used. ↩


 This post is for the C# developers out there and takes a look at the interesting conjunction of
This post is for the C# developers out there and takes a look at the interesting conjunction of  A few days ago, we published a new version of both the
A few days ago, we published a new version of both the  Hot on the heels of
Hot on the heels of 

 NeoSmart Technologies is pleased to announce the immediate availability of the latest additions to its Easy Recovery Essentials™ for Windows line of bootable repair and recovery tools for Microsoft Windows: EasyRE for Windows 11 and EasyRE Pro for Windows 11. Continuing a tradition that started with Windows 10, our Windows 11 boot recovery USB is currently available as a completely free download for anyone that needs to fix their Windows 11 installation after a virus infection or a Windows Update gone wrong.
NeoSmart Technologies is pleased to announce the immediate availability of the latest additions to its Easy Recovery Essentials™ for Windows line of bootable repair and recovery tools for Microsoft Windows: EasyRE for Windows 11 and EasyRE Pro for Windows 11. Continuing a tradition that started with Windows 10, our Windows 11 boot recovery USB is currently available as a completely free download for anyone that needs to fix their Windows 11 installation after a virus infection or a Windows Update gone wrong.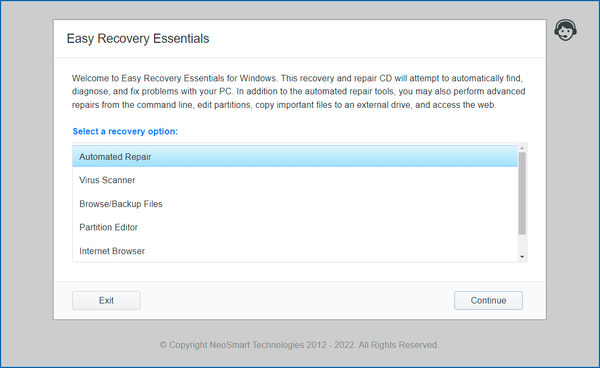
 Windows 11 is here and it comes with a new version of Segoe UI Emoji, the font that’s used across the OS to render various emoji from Unicode codepoint sequences to the emoji you see on screen (developers:
Windows 11 is here and it comes with a new version of Segoe UI Emoji, the font that’s used across the OS to render various emoji from Unicode codepoint sequences to the emoji you see on screen (developers: