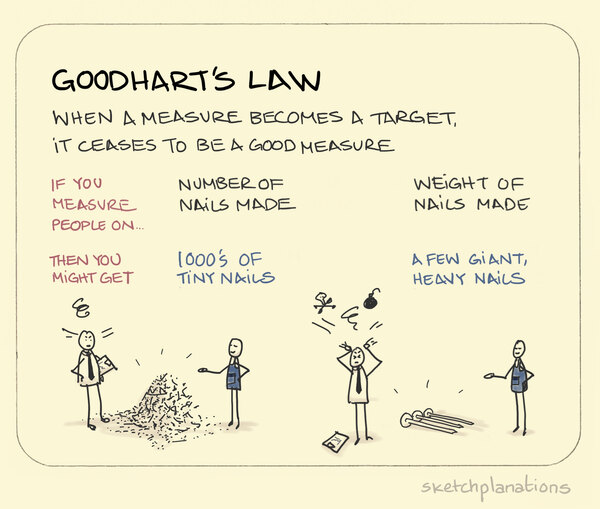
One nice thing that’s come about from the increased scrutiny that online security has been receiving is that it’s gone from being considered paranoid to becoming completely expected to be notified regarding incidents such as new logins, password changes, failed 2FA attempts, and other security-related activity. But any time a metric gets noticed, it also gets gamified and either decreases in value or ceases to be relevant altogether – a principal first documented by British economist Charles Goodhart and now known as Goodhart’s Law and demonstrated in this wonderful Sketch Plantations depiction:
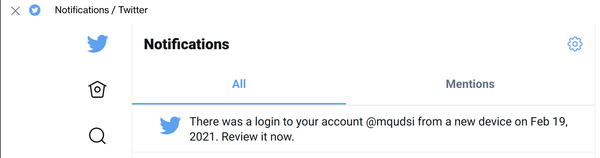
A year or two ago, twitter began alerting you when a login is first seen from a new device, even if two-factor login was used and the IP address is the same as a previously seen login attempt, a perfectly worthy attempt at increasing awareness of active sessions and logins. If someone scraped your email and password from the recent database dump omgkittens and discovered you’ve reused the same credentials on twitter, you’ll know that they logged into your account when you get an alert from twitter that looks like this:
That’s perfectly reasonable. They logged into your twitter, but they don’t necessarily have your email username/password and this gives you a chance to do something about it in case that wasn’t you (i.e. reset your password and start using a password manager with a unique password on each site).
But you’ll also get an in-app notification from twitter as soon as you someone’s logged in:
This alert will appear as an unread notification until whoever logged in to your account without your permission clicks on it and then it’ll eventually go away. In other words: it serves no purpose whatsoever besides getting you to click on the red/yellow notification icon to see your “notifications” inbox (so perhaps I’m actually being naive and this is in fact a dark pattern?) but it won’t serve any purpose because if you’ve hacked into an account, all you have to do is click the notification to make it go away.
It’s not impossible to make in-app “new login” notifications useful, but this isn’t the way to do them. For applications without access to a second form of notification that doesn’t involve using the app itself to notify the user (which doesn’t apply here since Twitter also sent an email), one such strategy is to wait some time (a few hours or a day) and then generate the in-app alert: chances are that the hacker isn’t still the one that’s logging into the account and won’t be the one to dismiss the alert this time around. Another option is to generate the alert when the account is next logged in to from an address/computer other than the one the app is alerting you about – which is downright obvious given that they clearly have and are able to use that very same information to generate this alert.

I absolutely hate it. I’m not an avid twitter user and this seriously makes me use it even less.
Just happened to me . Scarry
I have noticed that this happens on twitter, FB, etc and many other sites. I have cookies unblocked and I still get the new device everytime I log in
I don’t even have a twitter account but I still get these messages. What is happening? I have never even opened twitter to be honest. It is something of a snake pit anymore it seems. Anyways, how do I delete this? How would I be trying to login to an account I know nothing about? Why do these logins say they are in CA while I an in WA? Please help me!
@Aaron, someone has registered an account with your email address.
Unblock
How much time does the login notification state before it desapear?
Like 10 month?